System i Software
Next Step
Product Information
- iSecurity Overview
- iSecurity Action
- iSecurity Anti-Virus
- iSecurity AP-Journal
- PTF Tracker
- iSecurity Assessment
- iSecurity Audit
- iSecurity Authority on Demand
- iSecurity Capture
- iSecurity Central Administration
- iSecurity Command
- iSecurity Compliance Evaluator
- iSecurity Firewall
- iSecurity GUI
- iSecurity Native Object Security
- iSecurity Password
- Password Reset
- iSecurity Screen
- iSecurity Safe Update
- iSecurity System Control
- iSecurity User & System Value Replication
- iSecurity View
- iSecurity Visualizer for Audit
- iSecurity Visualizer for Firewall
- AP Journal
- Change Tracker
- DB Gate
- Filescope
- i4XML
- LinkIt
- View
- Window Menu
- VTLBackup4i
Assessment
Product Description
Raz-Lee Security's new Assessment module, part of the iSecurity suite, enables you to test your System i security vulnerability within minutes. Assessment checks your ports, sign-on attributes, user privileges, passwords, terminals, and more. Results are instantly provided, with a score of your current network security status with its present policy, compared to the network if iSecurity were in place. These results include colorful charts, a detailed written analysis, numerical score, and clear, easy-to-follow security recommendations.
Do you know how effective your System i security is?Unfortunately many companies don't. They tend to buy software after software, naively thinking that simply installing an expensive system provides all the protection they need. But it's not that simple. Every system MUST be checked for its efficiency on a regular basis.
The Assessment Solution
That's where Raz-Lee Security, developer of iSecurity, enters the picture. Based on years of experience working with and developing powerful software tools for the System i, our team of security professionals has created an interactive assessment report that allows you to test your System i vulnerability. This stringent security test assesses your security policies, and shows you - in a flash - exactly what your system strengths and weaknesses are.
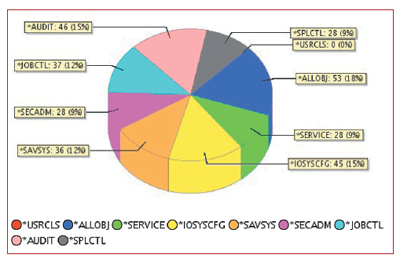
Colourful graphic displays provide easy reference and understanding
Assessment shows you:
- If your network is really protected
- If your ports are wide open to intruders
- If your sign on attributes are implemented properly
- If you have an excess of power users accessing your network
- If your auditing policies are performing as necessary
- How truly effective your network security would be by using iSecurity
- If your security policies adhere to IBM's protocols
- What the common denominator is for object authorities
- If your network is truly detecting security breaches in real-time
- If your system is Sarbanes-Oxley (SOX) - compliant
The Assessment Guarantee
Assessment comes certified by Raz-Lee Security for validity, precision, and accurate results, reflecting the definition and design expertise of System i security industry experts.
Features
- Performs a thorough System i vulnerability check
- Hyperlinks help you navigate through different sections of the report
- Provides colorful, graphically-displayed results
- Provides a detailed, written analysis of your network security policy
- Numerical scores to help explain results
- Covers user class, user privileges, system settings, exit points, signon attributes, password control, network protection, unattended terminals, and more
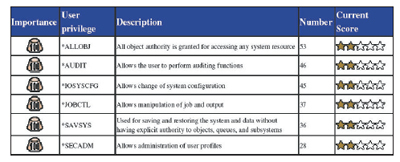
Structured tables provide easy-to-access reference and assesment scores
Benefits
- Easy-to-use: just download and begin
- Security check takes mere minutes
- Intuitive and easy-to-understand
- Raz-Lee certified for accuracy
- Comprehensive check of all facets of your system security
The software is available for a FREE Proof of Concept evaluation, for more details email [email protected] or call +61-3-9572-5869